Home
Next Level Cybersecurity
Risk Management
Cutting-edge cybersecurity solutions tailored to safeguard your business and valuable assets in industrial environments, ensuring unparalleled security and trust
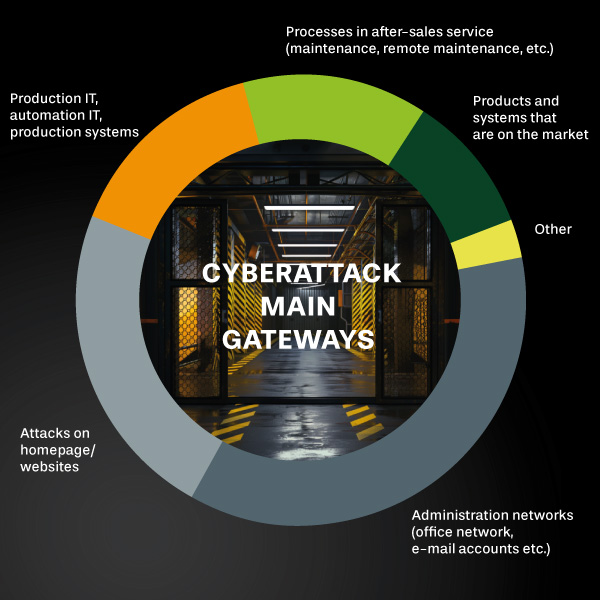
Cyber risks in industrial environments are on the rise.
Whether it’s deliberate attacks by activists seeking economic disruption or inadvertent targeting during geopolitical conflicts, the threats are real and growing.
Amidst the ongoing digitalization and the merging of IT and OT environments, regulatory obligations further underscore the need for proactive measures.
Our solutions are designed to support you with holistic Cyber risk management, to keep your devices updatable and to ensure compliance with legal requirements in the long term.
We tackle your industry’s challenges
Discover how our solutions provide security and protection for your business and valuable assets. Our services include not only cyber risk management, but also Device Update Management, Enterprise Engineering Support, Compliance Regulatory Readiness Consulting, and seamless deployment services.