
Cyber Threat Intelligence Becomes Mandatory: A New Priority for Critical Infrastructure
Cyber Threat Intelligence (CTI) is a major and massive growing discipline within Cybersecurity focusing on collecting, analyzing, and sharing information about current and potential cyber threats so organizations can anticipate, prevent, and respond to attacks more effectively according to Palo Alto Networks and other major players.
CTI is becoming a core capability for critical infrastructure operators like Energy providers, moving from “nice to have” to de facto and often legal requirements embedded in IT/OT/ICS security, NIS2 and national resilience strategies programs.

Specific Use Cases to critical infrastructure
Cyber Threat Intelligence (CTI) for critical infrastructures is trending toward more automation (AI/ML analytics over big data, OSINT, telemetry) and tighter integration into detection, response, and resilience planning, rather than standalone manual generated reports.
Critical infrastructures need an AI powered CTI engine to aggregate and interpret global Threats, to fuse it with proprietary models, enriched through the expertise of Cyber experts to get actionable insights and specific role based intelligence.
Introducing our AI based CTI approach for critical infrastructure.
CTI for critical infrastructure is trending toward more automation (AI/ML analytics over big data, OSINT, telemetry) and tighter integration into detection, response, and resilience planning, rather than standalone reports.
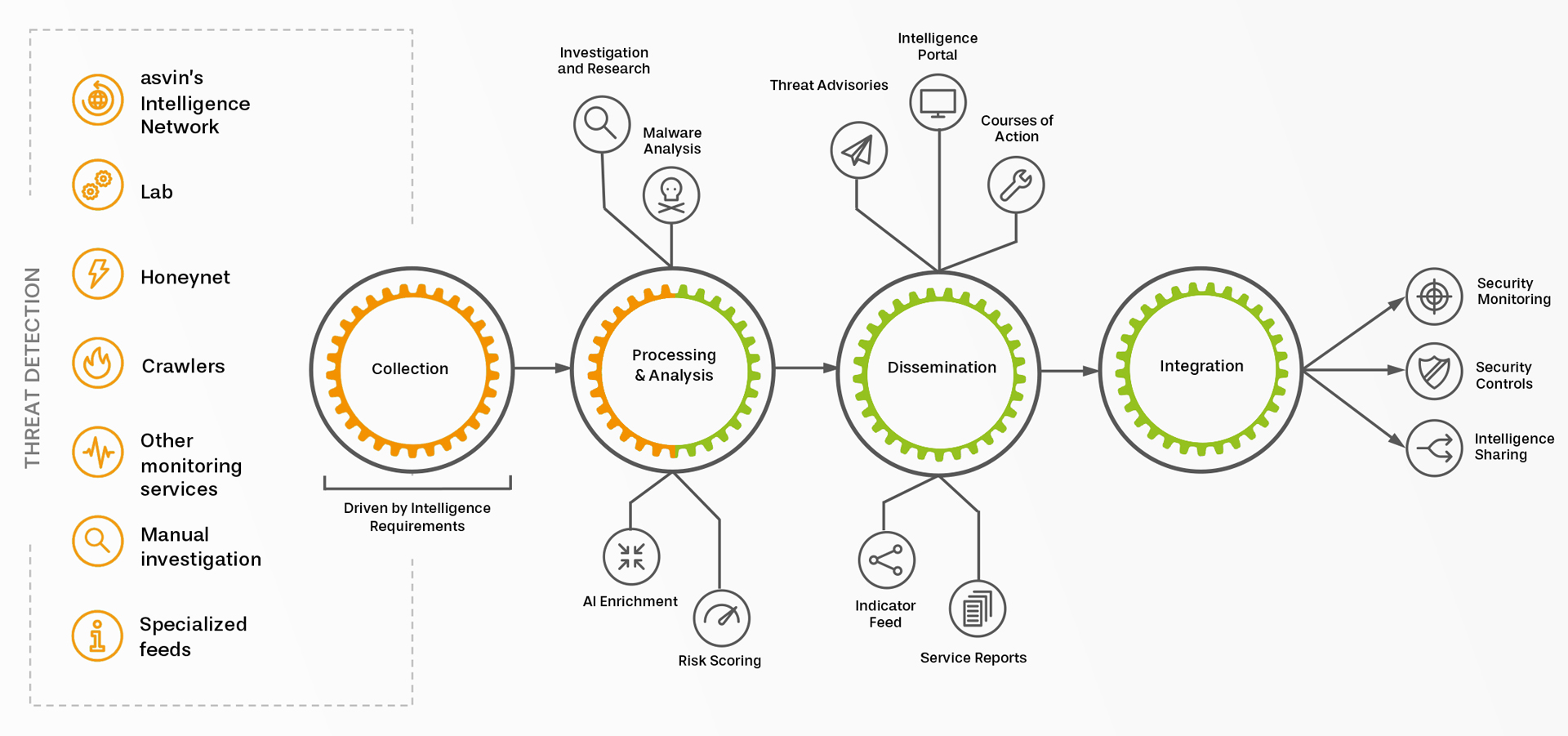
The graph shows the main elements of our AI powered CTI solution – turn fragmented CIT information into actionable insights and role base intelligence.
The right hand side shows the CTI feeds and sources for date collection. This list is not complete and needs to be adapted as Cybersecurity hreats are evolving very quickly. The core is processig and analytics, data will be analyzed, normanlized and enrichted by AI (Transformer and Foundational Models). The Dessimination provides CTI insights for different user und roles. The last one is the integration to exisiting workflows and IT tools.
This is the first article in a three-part series. The second introduces the role of AI in cybersecurity, and the third provides an overview of frameworks and how to prepare for the present and the future.






