Curious About the Challenges in Implementing Cyber Risk Management?
Explore the Key Challenges.
In today’s digital landscape, businesses are confronted with the daunting task of cybersecurity management. Meeting stringent industrial standards while keeping pace with a constantly evolving regulatory environment poses significant challenges.
Managing Standards and Regulations
From IEC 62443 and ISMS ISO 27001 to TISAX, the complexity can be overwhelming. Additionally, the ever-growing array of cybersecurity laws like the Cyber Resilience Act, EU NIS2 Directive, Radio Equipment Directive (RED), and the European AI Act further complicates matters.
Balancing Efficiency with Compliance
A critical challenge lies in achieving optimal cyber risk management without overburdening skilled employees or sacrificing precious time during the implementation process. Without professional guidance, businesses risk inefficient deployment, potential security vulnerabilities, and decreased productivity.
Streamlining Cybersecurity Management with Expertise
At asvin, we recognize these obstacles and provide comprehensive services to streamline cybersecurity management systems. Our expertise guides you effortlessly towards compliance, ensuring the security of your operations while maximizing efficiency.
Cyber Threats Escalate Across Industries.
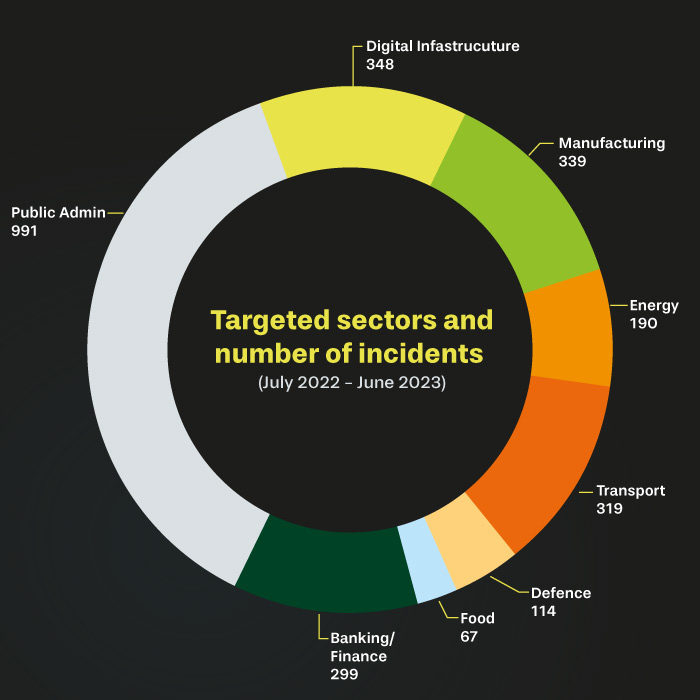
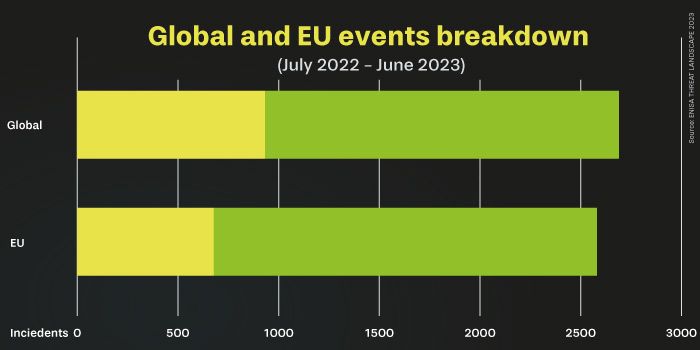
In today’s digital realm, cyber threats are escalating rapidly year after year. These threats permeate diverse sectors, spanning manufacturing, energy, digital infastructure and more, underlining the pervasive nature of cybercrime.
As cyber adversaries evolve, so must our defenses. The sectors highlighted in our infographic stem from the classification of the EU NIS 2, offering a snapshot of the varied industries under siege.
Yet, amidst these challenges, there lies an opportunity for collaboration. Cybersecurity teams require robust partnerships to navigate this ever-shifting landscape effectively. Without such alliances, staying ahead of emerging threats becomes a daunting task.
In essence, the battle against cyber threats demands collective action. By fostering strong partnerships, we empower cybersecurity teams to proactively defend against evolving risks, ensuring a secure digital future for all.
We tackle your industry’s challenges
Discover how our solutions provide security and protection for your business and valuable assets. Our services include not only cyber risk management, but also Device Update Management, Enterprise Engineering Support, Compliance Regulatory Readiness Consulting, and seamless deployment services.













