Targeted cyber risk management is essential for focusing on the truly relevant threats and risks – and we’re here to support you.
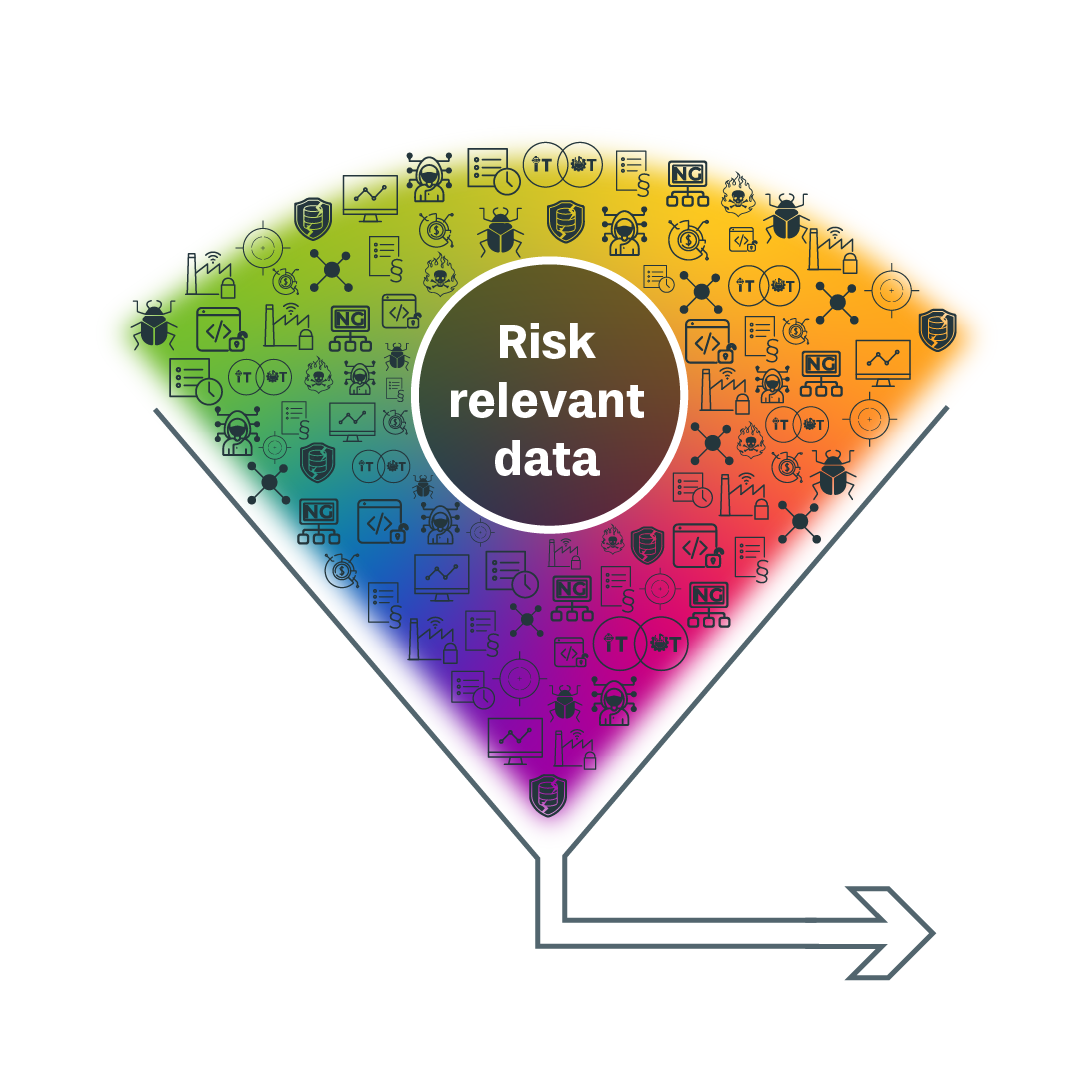
Modern industrial and critical infrastructure organizations are overwhelmed by data: countless assets, ever-growing vulnerability reports, and not enough hands to respond. Traditional tools scan – but don’t guide. They miss one thing: context.
Risk by Context™ – Cyber Security Risk Management combines AI, graph analytics and topological mapping to model your cyber risk in full business context – even when data is incomplete.
It’s not just about seeing cyber risks – it’s about understanding them in context.
Why organizations choose Cyber Risk Management with Risk by Context™
Our clients benefit from advanced cybersecurity decisions, achieved through enhanced prioritization capabilities and methods – enabling them to rise above potential threats or minimize less critical ones
Think of cyber risks as part of your general business risks
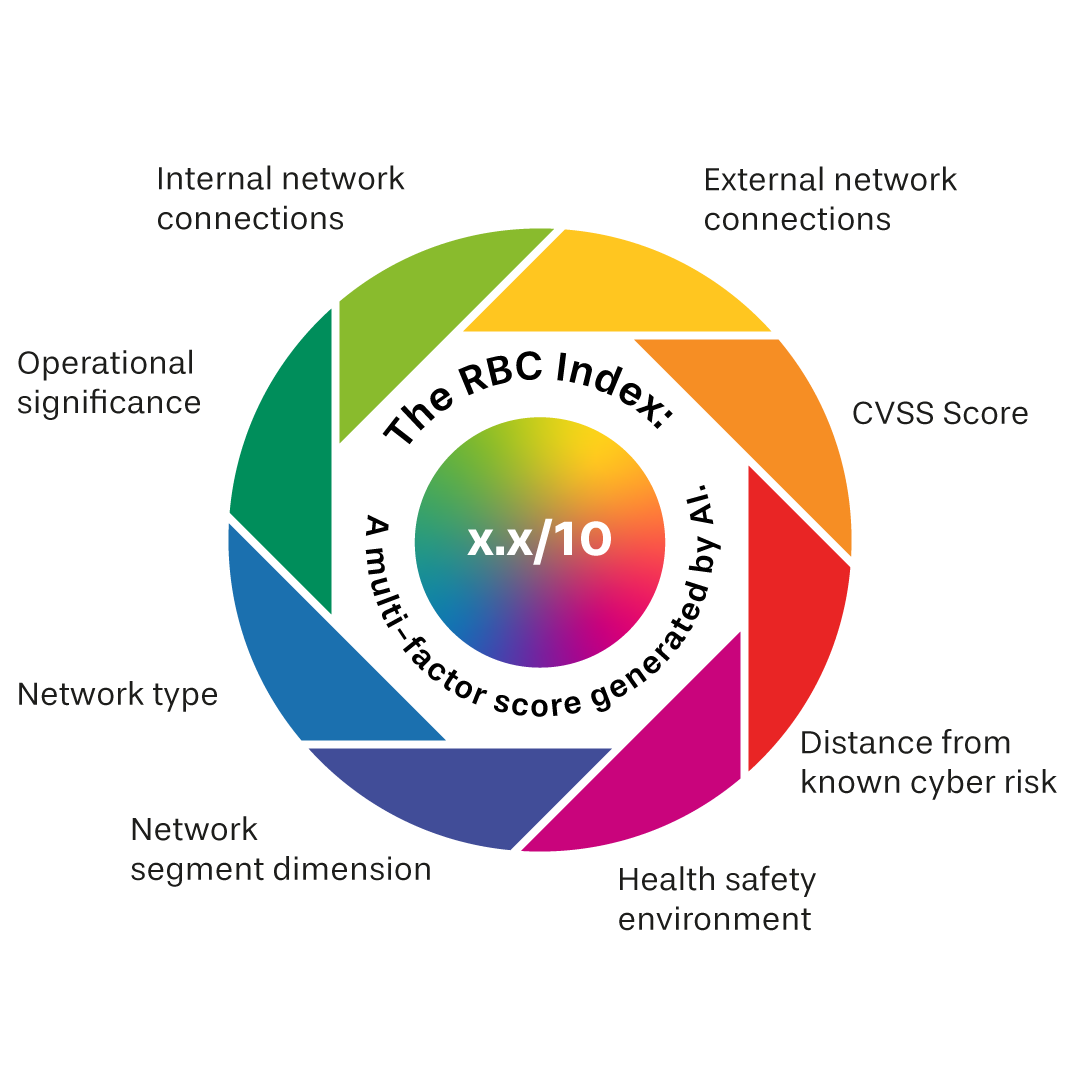
Our AI-powered solution utilizes a variety of existing cybersecurity metrics, network and asset data, as well as other crucial business data to create the Risk by Context (RBC) Index. By analyzing your digital infrastructure and its dependencies, you can accurately evaluate the risks associated with your business and make informed decisions to safeguard against potential threats.
Get the big picture in seconds
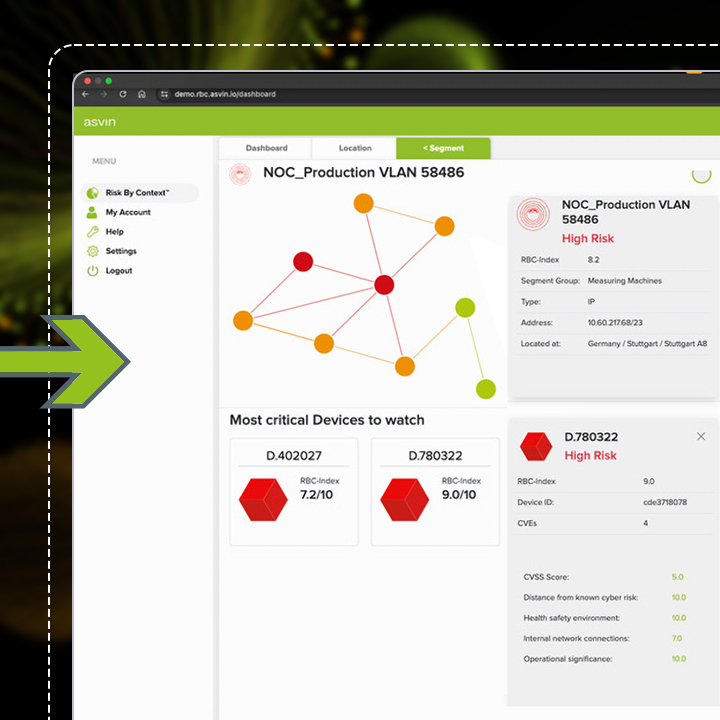
The graph visualization displays the risk level of every location, along with their interconnections.
Your most critical locations to watch are displayed on info cards for quick access to deeper levels.

Initial dashboard shows whole organization

Sample Dashboard of a specific Location
Explore further and discover where to head.
At the location level, you can easily view all network segments and their cyber risk status, so the responsible parties can know what requires attention.
Go into detail and find the root cause
At the segment level, you get detailed insights into each individual asset, their connections to each other, and the rating of the individual context elements. These insights are used to create the Risk by Context Index.
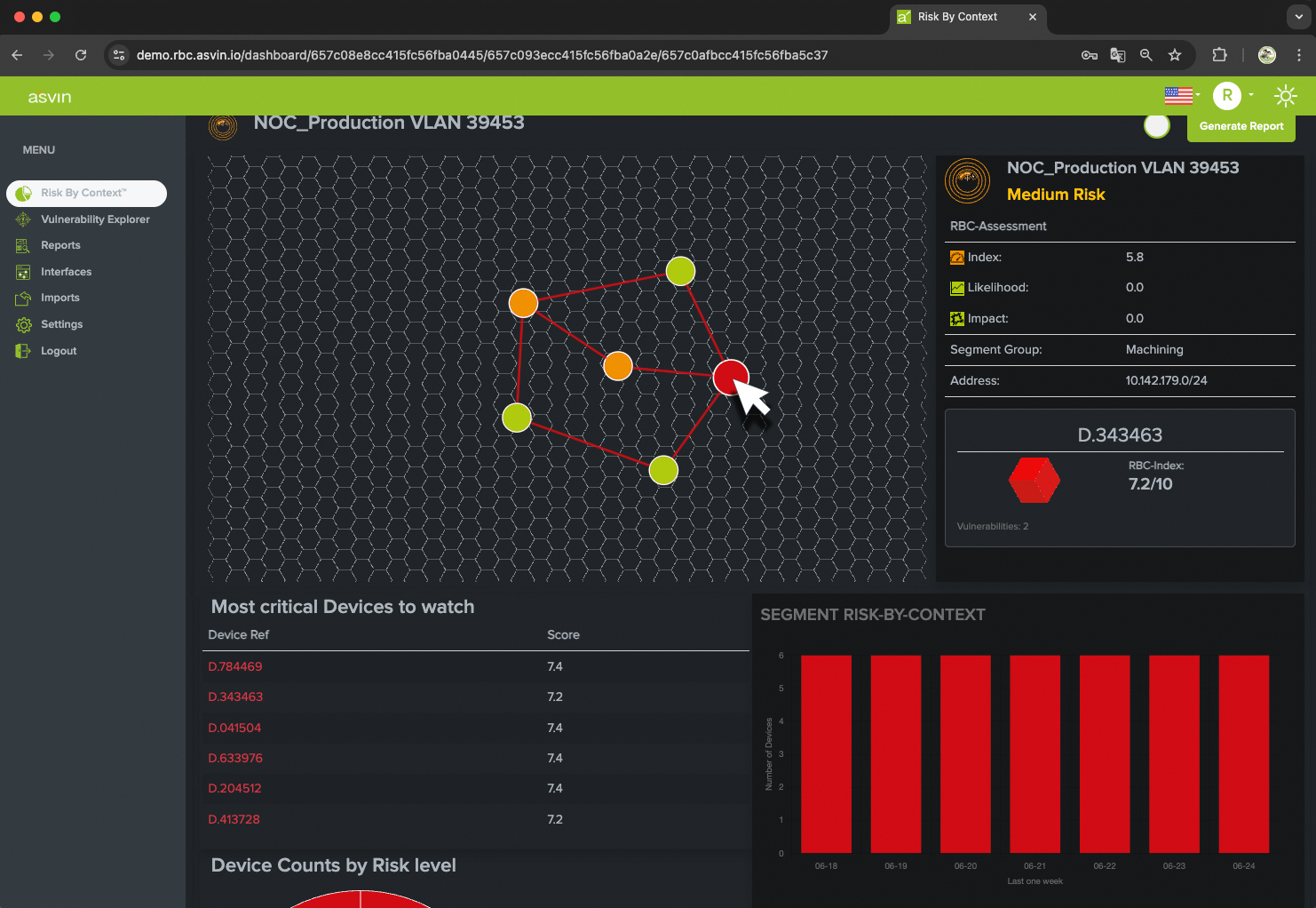
Sample Dashboard of a specific Networksegment inside a Location