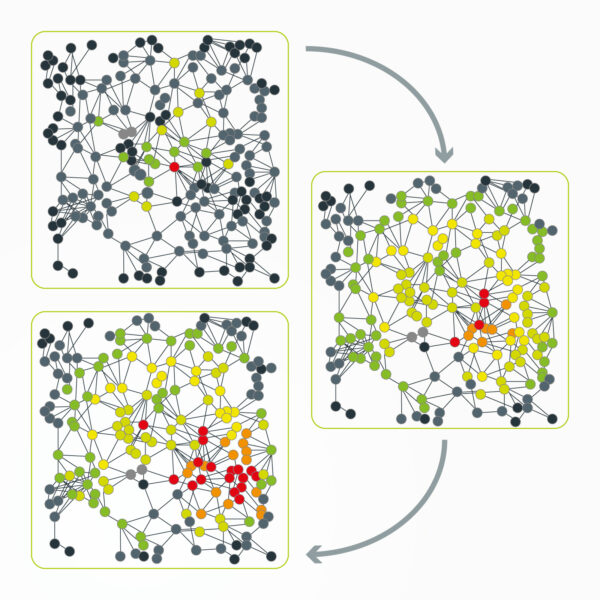
Simulation of Enterprise Architecture towards Cyber Resilience based on Investment strategies and focus of spendings and resources
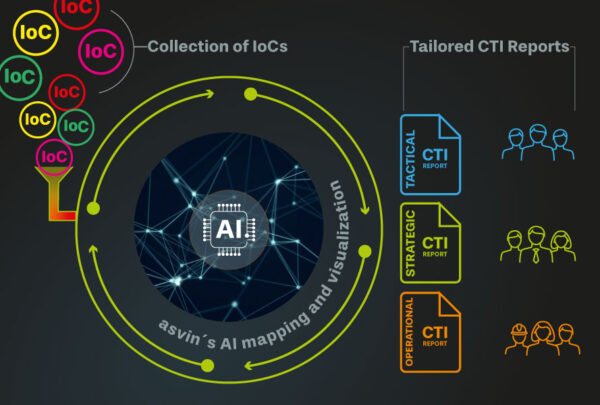
Automated CTI processing
Automated processing and distribution of security advisories significantly improves the speed of response to new cyber threats. Available information is tailored to the needs of individual stakeholders and visualised using asvin’s AI reporting. This increases understanding of the threat situation and reduces response time.
asvin’s CTI processing enables
Cyber resilience analysis and forecasting
Cyber resilience describes an organisation’s ability to minimise the impact of cyber incidents and restore operational systems to maintain business continuity. This must be achieved within a limited time frame and budget.
asvin Labs works with international research institutions and experts to develop analysis and prediction models to measure cyber resilience.