Cybersecurity in Factory Automation: Why IT Security Concepts Are Not Simply Transferable
Cybersecurity is not a one-size-fits-all concept…
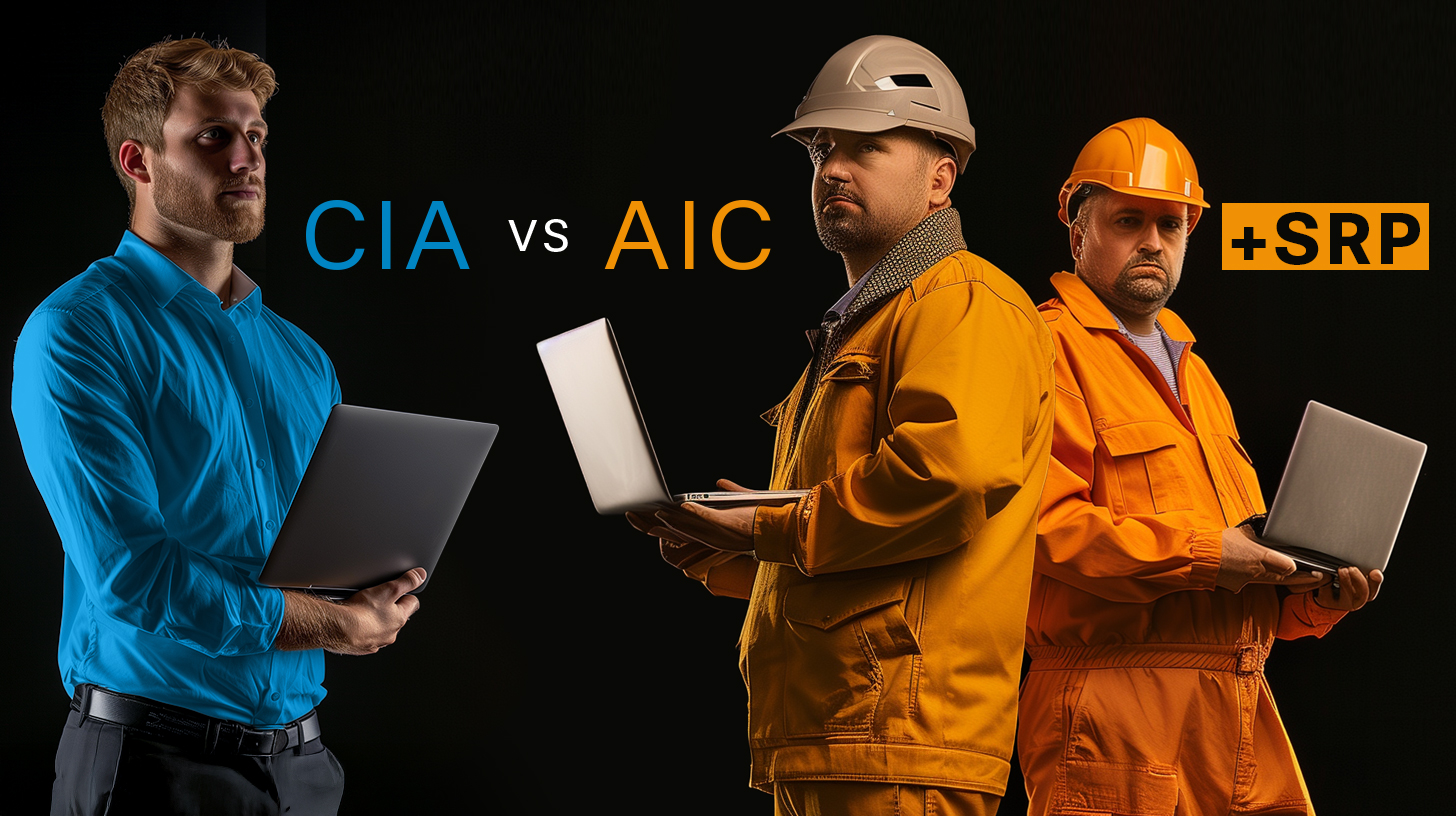
… especially when it comes to securing IT, OT, and ICS systems. While IT security focuses on the CIA triad (Confidentiality, Integrity, Availability), OT security prioritizes the AIC triad (Availability, Integrity, Confidentiality). In industrial control systems (ICS), the SRP triad (Safety, Reliability, Productivity) becomes the key focus. These varying priorities highlight why traditional IT security approaches fall short in factory automation and why new, specialized solutions are necessary.
The Three Triads Compared:
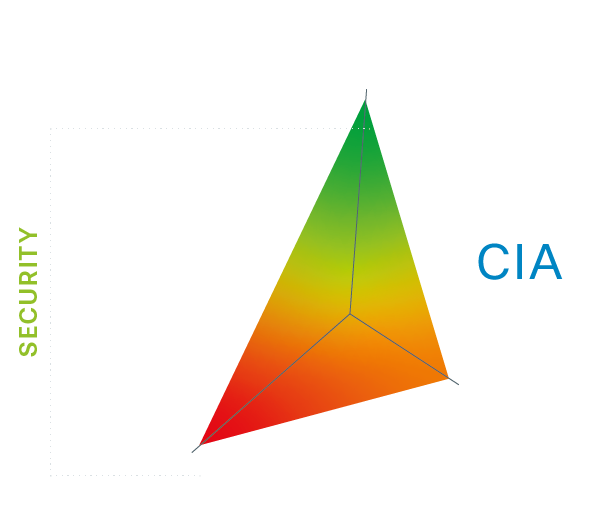
CIA Triad (IT Security)
- Confidentiality: Protecting sensitive data from unauthorized access.
- Integrity: Ensuring the authenticity and accuracy of data.
- Availability: Ensuring systems and data are always accessible.
In traditional IT security, protecting data is the highest priority.
AIC Triad (OT Security)
- Availability: Production processes must not fail.
- Integrity: Processes and controls must operate flawlessly.
- Confidentiality: Protecting trade secrets, but not at the expense of availability.
In OT (Operational Technology), the continuous availability of systems is the top priority.
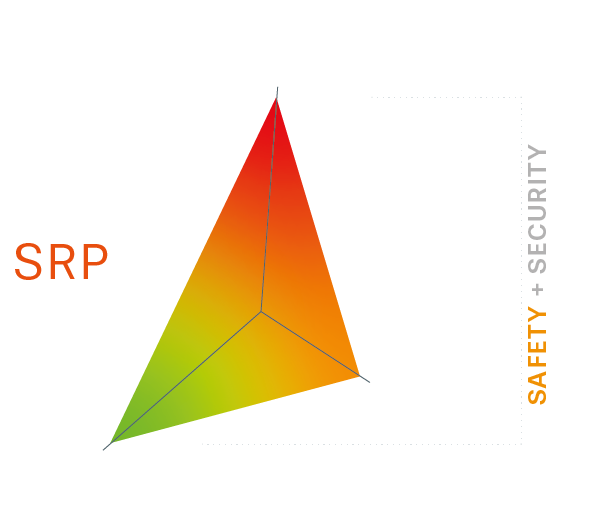
SRP Triad (ICS Security)
- Safety: Protecting people and machines from hazardous situations.
- Reliability: Maintaining stable and predictable operating conditions.
- Productivity: Maximizing efficiency without unplanned downtimes.
In industrial control systems (ICS), protecting people and machines is the central focus.
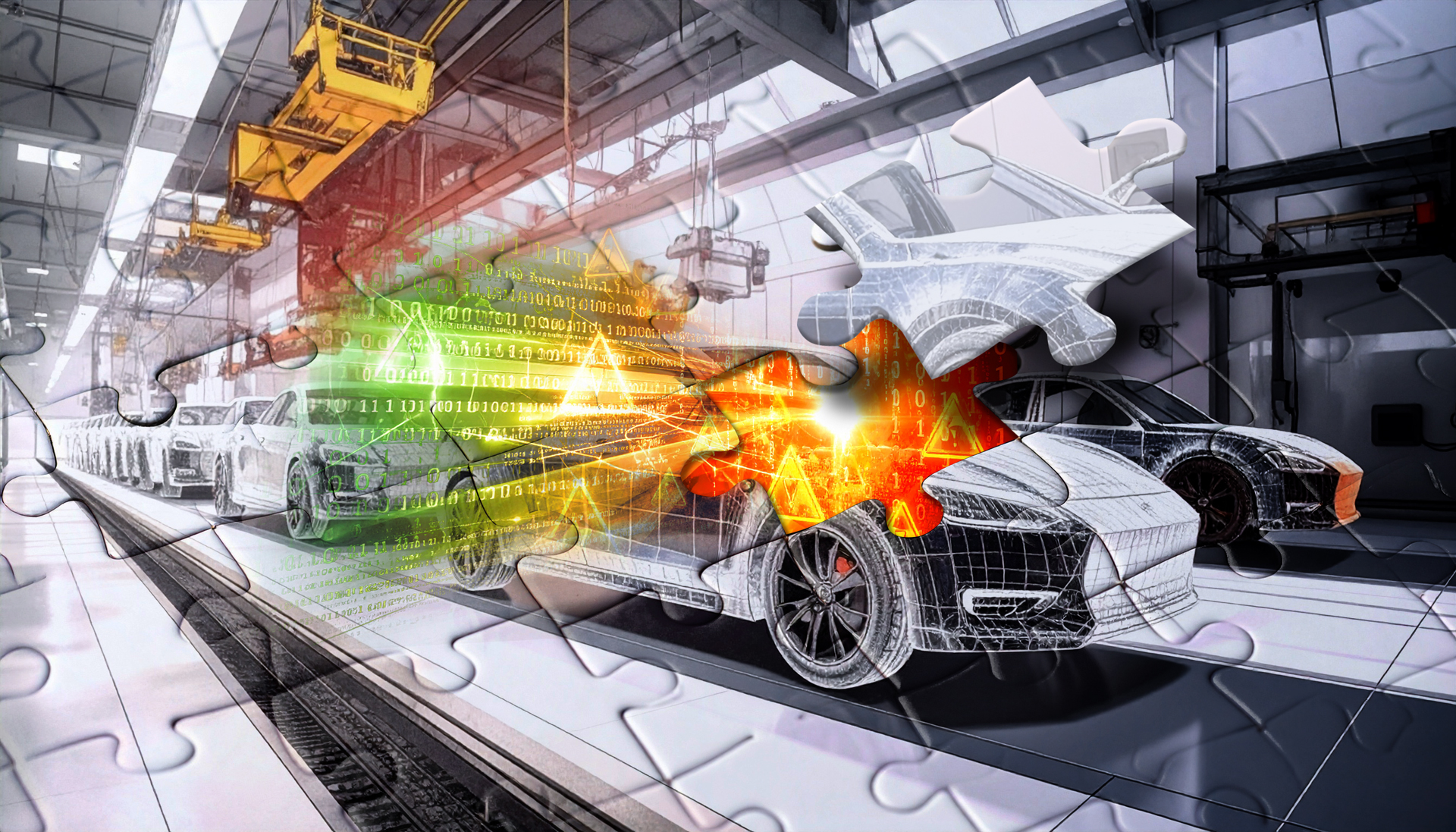
Why a Different Cybersecurity Approach Is Necessary in Factory Automation
In IT, a compromised server can be quickly isolated or reset. In a production environment, this is not as simple: a failure or a misprogrammed control command can cause significant economic damage or even jeopardize lives.
•Patching & Updates:
While IT systems are regularly updated, many OT and ICS systems are decades old and cannot be easily patched.
•Network Architecture:
IT systems are often segmented and cloud-based, whereas OT networks tend to have flat structures and cannot tolerate high latency.
•Threat Models:
In IT, data loss and ransomware are major threats, while in OT, physical manipulation and system failures pose the greatest risks.
How asvin Optimizes Cybersecurity for Factory Automation
asvin offers specialized solutions tailored to the unique requirements of OT and ICS security:
•Risk by Context™: An adaptive risk management approach that adjusts to the specific needs of OT and ICS. Instead of just scanning for vulnerabilities, we analyze the contextual impact of threats on production processes.
•Device Security Booster™: A secure update management solution for industrial control systems that works with legacy systems and minimizes downtime.
•Cybersecurity Expertise as a Service: Consulting and implementation of security strategies that focus not only on IT but also on OT and ICS.