Factory Automation
Cybersecurity for
Factory Automation
Protect your production with asvin industrial cybersecurity solutions and manage & prioritize cyber risks in your operating technology.
Safeguard your connected devices throughout their lifecycle and prioritize your investments in risk reduction.
The Challenge: Security Risks in Industrial Factory Automation
The increasing connectivity of production systems brings significant cybersecurity risks. Legacy systems, expanding attack surfaces, and targeted cyberattacks threaten operational continuity and can lead to severe financial damage.

The Solution: asvin as Your Cybersecurity Partner for Factory Automation
asvin delivers targeted solutions to mitigate security risks and build a resilient OT environment. Our innovative technologies protect industrial automation systems and support compliance with regulations like NIS-2.
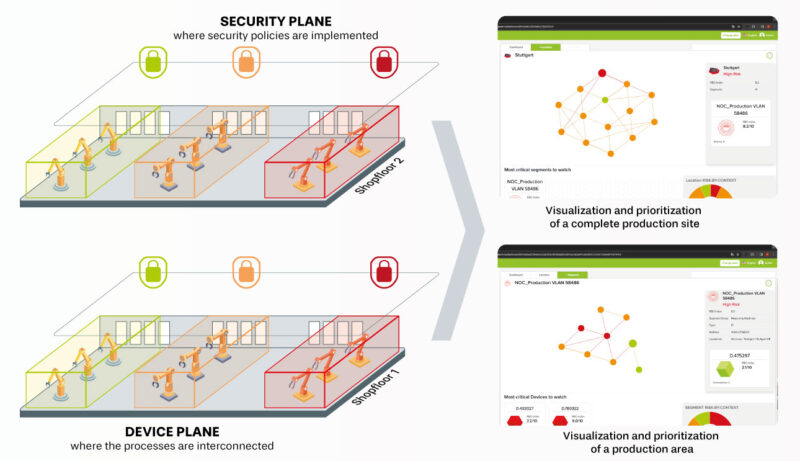
Risk By Context™ shifts from static CVSS-based assessments to a dynamic model that integrates context,
system interdependencies, and predictive elements for cyber resilience in complex OT/IT environments.
Our Approach:

Your Benefits with asvin
By partnering with asvin, your company gains: